
Data Privacy in the Age of AI: Why Training Quality Matters More Than Ever
Generative AI is changing data privacy and cybersecurity. Discover how training, phishing simulations, and awareness reduce AI-driven risks.

Picture this eye-opening scenario……A delivery driver wearing recognizable attire entered the lobby carrying a seemingly heavy package. Approaching the entrance, he appeared stressed but clearly tried to put on a friendly face. Instinctively, an employee held the door open to help. The receptionist glanced at the courier ID badge and handed over a visitor pass without hesitation.
Security cameras later revealed something troubling. Moments after entering, the supposed driver tossed aside the now obviously empty box and slipped into an empty office. He quickly inserted a USB device into the network switch. Seconds later, screens flickered, phones disconnected, and servers went offline entirely. Business operations stopped, leaving employees staring helplessly at blank screens.
We typically think of social engineering in terms of phishing and cybersecurity. But this scenario illustrates another way
criminals use social engineering to exploit vulnerabilities. In this case, the criminal capitalized on the human tendencies to be polite and trusting. Attackers also often exploit power dynamics by posing as someone in a position of authority (wearing a visibility vest, a hard hat, and carrying a clipboard, for example). And there are countless other ways in which criminals leverage emotions of fear, urgency, and familiarity to gain entry.
Many organizations still treat physical and cybersecurity as separate issues, despite clear evidence urging integration. According to the ASIS Foundation (2024), over 60 percent of organizations have now partially or completely integrated their physical and cybersecurity operations, with 76 percent reporting a stronger overall security posture as a result. Allied Universal’s 2025 World Security Report highlights that nearly 90 percent of businesses recognize cyber threats as serious physical risks, noting a 146 percent increase in physical disruptions caused directly by cyberattacks within the past year alone. The message is clear: physical and cybersecurity must be unified for effective defense.
Consider a scenario involving a major enterprise, where physical tampering with critical infrastructure led to an unexpected 48-hour operational outage. The breach caused immediate disruptions to core business activities, resulting in
significant financial losses due to halted operations and an immediate stock value decline. Although specific financial figures remain confidential, the impact was tangible: employee productivity halted, investor confidence was shaken, and substantial costs incurred to restore operations and reassure stakeholders. Industry benchmarks underscore the severity of the problem: according to Aberdeen Research, unplanned downtime can cost organizations up to $260,000 per hour, with average breach costs globally now approaching $4.88 million. Physical breaches are not just physical; they can quickly escalate into critical business risks, which is why integrating physical and cybersecurity is such an urgent priority.
Does your current physical security training truly prepare employees, or is it simply fulfilling compliance requirements? Ask yourself:
Customized training fosters meaningful engagement and builds lasting habits, helping to embed security awareness into your organization’s culture and strengthen your defenses.
If your employees struggle to confidently answer these questions, your organization might be more vulnerable than you realize.
If your current training doesn’t clearly reflect your organization’s unique risks and entry points, could a more customized approach better protect your business?
For example, including images of your organization’s actual ID badges and visitor passes could be a simple tweak to an off-the-shelf course that could help employees engage with and retain protocols for secure entry.
Consider how implementing a customized physical security training program, designed specifically for your organization, can significantly improve your security posture. By intentionally aligning your physical security and cybersecurity teams, your organization can respond faster to threats, share critical insights, and proactively identify vulnerabilities that neither team would easily detect alone. This unified approach makes your organization significantly more resilient against breaches, whether physical or digital.
This collaborative training approach not only aligns directly with your organization’s policies but also creates lasting behavioral change and builds a culture of integrated security awareness.
GLS is a recognized leader in customized cybersecurity awareness training. Whether it’s creating a course entirely from scratch, incorporating your policy, including images or guidelines specific to your organization, or something else, our goal is to ensure your training truly moves the needle. Our specialized approach can help bridge the gap between your physical security and cybersecurity teams, resulting in a comprehensive, cohesive program that places your organization among the hardest targets in your industry.
Isn’t it time your security awareness training worked as hard as you do?

Generative AI is changing data privacy and cybersecurity. Discover how training, phishing simulations, and awareness reduce AI-driven risks.

Fraud is changing faster than most defenses, and awareness alone is not enough. Organizations must now combine artificial intelligence, process controls, and human intuition to stay ahead.

As artificial intelligence reshapes our digital world, it’s also transforming the cybersecurity landscape — for better and for worse. This Cybersecurity Awareness Month, explore how AI is revolutionizing threat detection and defense, while also empowering cybercriminals to craft more convincing attacks. Learn why awareness, responsibility, and human oversight are key to staying secure in the age of intelligent technology.

Cybersecurity Awareness Month should be more than a checkbox—it’s a chance to build a lasting security culture. Many employees remain unaware of CSAM, but participation drives engagement, vigilance, and measurable ROI.
GLS helps organizations transform CSAM into year-round impact with customized campaigns, gamified learning, and tailored training that turn awareness into action.

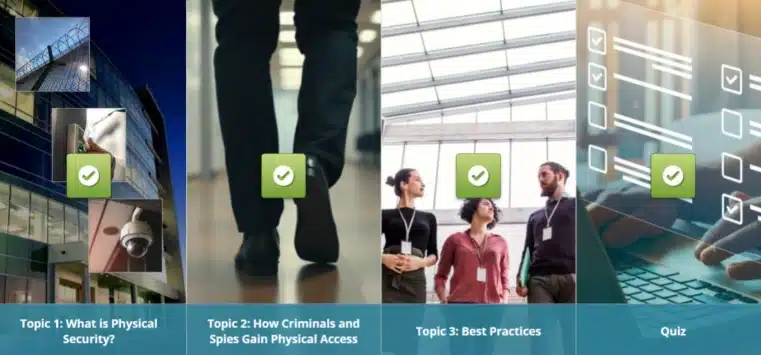
Discover why integrating physical security and cybersecurity training is critical. Learn how customized eLearning scenarios using your own facility images can strengthen defenses and build lasting security awareness.

Cyber threats are rising—pair cyber insurance with awareness training for stronger protection, compliance, and business resilience.
